The Shadow Economy of Zero-Days
- Z-ONE TEAM
- Apr 7
- 4 min read
THE COI
01 About Primary Sector
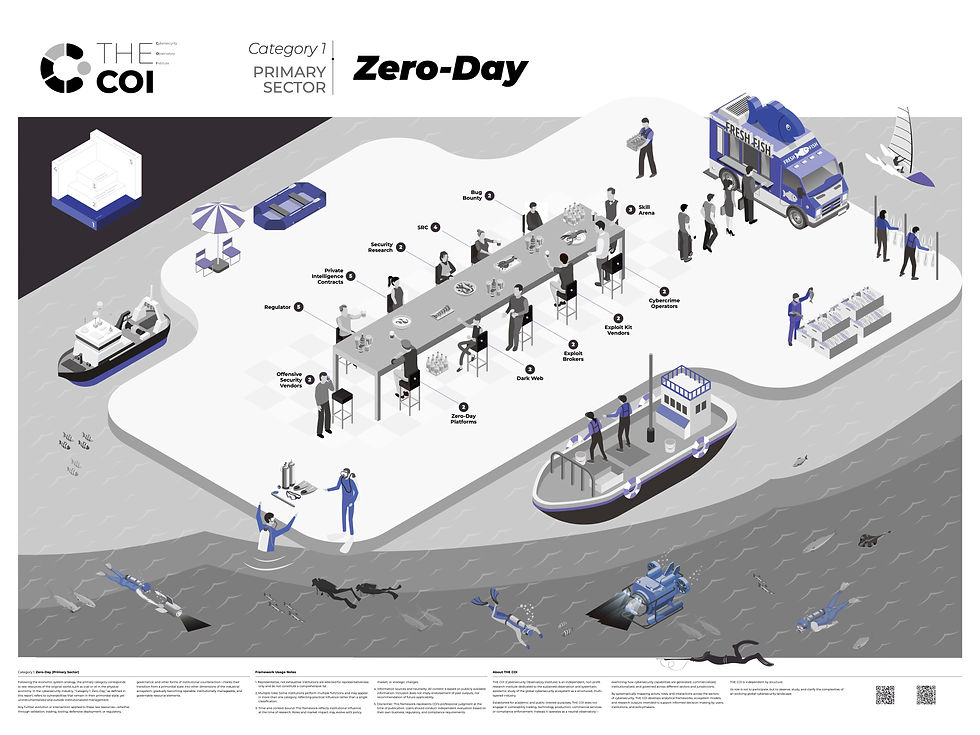
Category 1: Zero-Day (Primary Sector)
Following the economic system analogy, the primary category corresponds to raw resources of the original world, such as coal or oil in the physical economy. In the cybersecurity industry, “Category 1: Zero-Day,” as defined in this report, refers to vulnerabilities that remain in their primordial state, yet uninstrumentalized and outside institutionalized management.
02 Structural Characteristics of the Zero-Day Shadow System
Primordial Industrial Foundation
Zero-day vulnerabilities constitute the primordial foundation of the industrial system. They are not a derivative or incidental phenomenon of cybersecurity, but rather the very condition of its existence: without vulnerabilities, there would be no notion of security. It is precisely the persistent existence of vulnerabilities that renders possible the entire spectrum of defensive, detection, and exploitative activities, thereby defining the generative logic and existential boundaries of the industry as a whole.
Risk as a Function of Relational Use
Risk is not inherent to the vulnerability itself, but is generated through the ways in which different actors relate to and utilize it. As a neutral technical entity, a zero-day vulnerability derives its properties from the pathways of use and behavioral structures into which it is embedded. Within this process, researchers, platforms, vendors, underground actors, regulators, and various end-users together form a densely interwoven multi-actor network. Within this network, vulnerabilities are continuously processed, transformed, and re-applied, giving rise to highly complex patterns of interaction. Consequently, both risk and value are not determined by the technical artifact itself, but are produced through the structure and evolution of relational dynamics.
Stochastic Discovery and Temporal Decay
Zero-day vulnerabilities exhibit the characteristics of highly time-sensitive assets, whose effectiveness and operational scope undergo rapid decay. Once disclosed or patched, their exclusivity and exploitability diminish sharply. At the same time, their supply is shaped not only by individual expertise and accumulated experience, but also by an inherent degree of stochasticity: the emergence and discovery of vulnerabilities are not fully predictable, nor can they be reliably reproduced through standardized processes. This dual condition—dependence on individual capability combined with stochastic discovery—renders the supply structurally scarce and resistant to scalable production.
Dual-Track Operation and Ambiguous Legitimacy
The system operates along parallel “above-ground” and “underground” tracks, within which the same technical artifacts circulate and transform across compliant and non-compliant environments. The boundary between legality and illegality is not discrete, but instead manifests as a continuum. The same act may be assigned entirely different meanings depending on jurisdictional context, institutional frameworks, and intended use. As a result, the boundaries of the system remain inherently dynamic and indeterminate.
Trust Dependence and Value Dispersion
The functioning of the system relies heavily on non-transparent market relations, within which information is asymmetrically distributed among participants. Transactions are grounded more in trust, channels, and accumulated experience than in unified and publicly observable pricing mechanisms, resulting in a pricing structure that is both opaque and highly dispersed. Pricing is jointly determined by use-case context, exclusivity of the asset, and the nature of the buyer, and diverges across segmented sub-markets into fragmented and non-uniform structures. At the same time, value distribution across the industrial chain is markedly asymmetric: vulnerability discoverers typically capture one-off returns, whereas actors engaged in utilization and transformation may extract sustained and compounding economic gains.
03 Notes
Premise of the Analysis
THE COI analytical model is constructed to observe the various roles within the cybersecurity ecosystem and the relationships among them. The model itself is an abstract structure: its function is to reveal relationships, not to render moral judgment.
Yet any analysis must proceed within a concrete setting. Only through the articulation of a scenario can relationships become clear, meaning emerge, and discussion take place.
In examining the roles and relations of the secondary industry, we therefore introduce a default assumption: the discussion concerns the classification of roles within the commercial secondary sector of cybersecurity industry, and the relationships among them.
In fact, upon the same primary foundation—Zero-Day—different forms of secondary industries may arise. One may observe, for example, a black-market cybercrime sector, or a state-oriented cyber capability shaped by political objectives.
When the underlying assumption changes, the roles within it change as well, and so too do their relations to the other dimensions of the model.
The Non-Attribution of Individuals
This framework does not assign categorical attribution to individuals themselves. The underlying rationale is that individuals constitute highly fluid variables rather than stable industrial roles. A person’s skills, identities, and behaviors may fall into different categories depending on time, context, and mode of engagement.
For instance, a highly skilled security researcher may, during working hours, operate as part of an enterprise or government demand-side organization under Category Four, or as an employee of a technology vendor under Category Two, conducting compliant research and development. Outside formal work contexts, the same individual’s technical activities may fall within Category One, involving the discovery and analysis of Zero-Day vulnerabilities, and in some cases, their circulation
04 About THE COI
THE COI (Cybersecurity Observatory Institute) is an independent, non-profit research institute dedicated to the sustained observation and systematic epistemic study of the global cybersecurity ecosystem as a structured, multi-layered industry.
Established for academic and public-interest purposes, THE COI does not engage in vulnerability trading, technology production, commercial services, or compliance enforcement. Instead, it operates as a neutral observatory—examining how cybersecurity capabilities are generated, commercialized, institutionalized, and governed across different sectors and jurisdictions.
By systematically mapping actors, roles, and interactions across the sectors of cybersecurity, THE COI develops analytical frameworks, ecosystem models, and research outputs intended to support informed decision-making by users, institutions, and policymakers.
THE COI is independent by structure.
Its role is not to participate, but to observe, study, and clarify the complexities of an evolving global cybersecurity landscape.
Subscribe and get the research report HERE.
Contact THE COI
info@the-coi.org




Comments